The Secure Web Based Tool 2102204343 offers authenticated remote task access with defined governance and responsibilities. Its core defenses center on encryption and strict access controls, separating data handling from permissions. Real-time monitoring, dashboards, alerts, and audit trails support ongoing compliance across modular components. The architecture favors incremental rollout and reproducible environments, enabling scalable collaboration. The discussion will probe how these elements translate into reliable operations and what trade-offs they entail for teams and governance.
What Is Secure Web Based Tool 2102204343 and Why It Matters
Secure Web Based Tool 2102204343 refers to an online software solution designed to perform secure operations through a web interface. The tool facilitates remote tasks while introducing specific security risks and governance considerations. It emphasizes user authentication as a foundational requirement, ensuring legitimate access. By delineating scope, capabilities, and responsibilities, it clarifies why reliable access controls and transparent workflows matter for freedom-informed use.
How Encryption and Access Controls Protect Your Data
Encryption and access controls are the primary lines of defense for data within Secure Web Based Tool 2102204343.
The approach separates data handling from access rights, reducing exposure.
Encryption best practices ensure confidentiality while stored and transmitted information remains protected.
Access control models define roles, permissions, and enforcement mechanisms, supporting granular data governance and user accountability without compromising operational freedom.
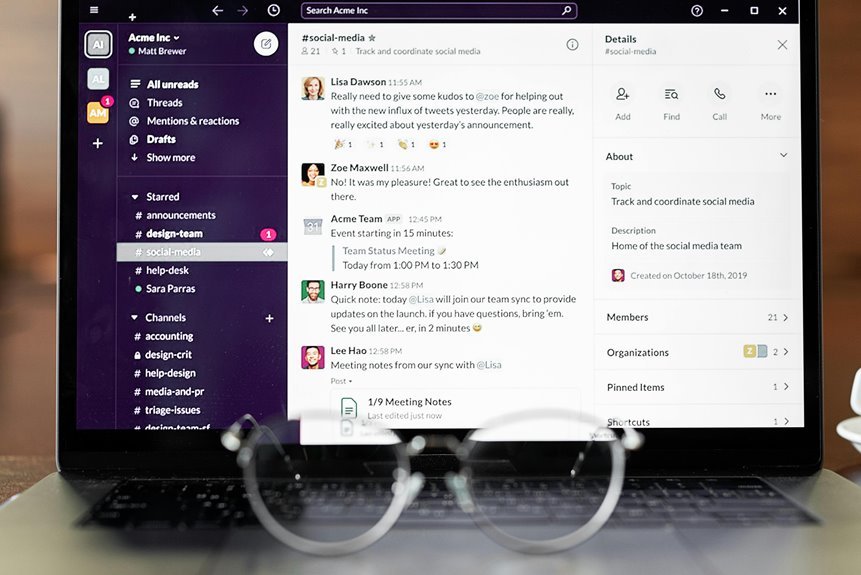
Real-Time Monitoring and Compliance Features in Practice
Real-time monitoring and compliance features in practice provide continuous oversight of data flows, system activity, and policy adherence within Secure Web Based Tool 2102204343. It emphasizes real time monitoring dashboards, alerting, and audit trails, supporting rapid incident response.
Compliance features integrate encryption access governance, role validation, and policy checks, while modular deployment enables configurable controls without compromising overall security posture.
Scalability and Deployment: Modular Design for Teams of Any Size
Scalability and deployment for Secure Web Based Tool 2102204343 embrace a modular design that accommodates teams of any size by enabling configurable components and scalable governance. The architecture supports scalability considerations through decoupled services, standardized interfaces, and on-demand resource provisioning. Deployment strategies emphasize incremental rollout, collaborative governance, and reproducible environments, ensuring consistent performance while empowering teams to tailor configurations without compromising security or integrity.
Conclusion
The Secure Web Based Tool 2102204343 presents a poised paradox: rigorous security with accessible collaboration. Juxtaposing airtight encryption and open, real-time dashboards, the platform merges protection with transparency. While governance and audit trails enforce discipline, modular design invites agile teamwork and scalable growth. In practice, security does not suppress speed; it clarifies it. The result is a dependable, adaptable environment where trust and efficiency reinforce one another, enabling reliable remote tasks without compromising performance.